The difference may sound subtle, but it can cause unrecoverable damage to organizations. Triggered by intentional (or unintentional) employee behavior, insider risk puts business data integrity at stake, while insider threat happens when the data at risk gets exposed to some unauthorized entity. Both cases pose challenges to workplace compliance and operational efficiency. So, how insiders can cause problems for businesses and what are the effective measures to control them – let’s further discuss.
Table of Contents
The trusted members in organizations are hard to suspect and can take advantage of their privileged positions to cause data and reputation damage to businesses, especially with information-intensive operations. Insiders are hidden risks waiting for time and opportunity to grow into threats and harm companies with critical business details.
Insider risks vs threats – What differs one from the other
The intentional (or accidental) non-compliant employee behavior against the business policy and security standards is an insider-caused risk, and if it harms businesses with data, monetary, or reputation loss, it transitions into insider threats. Insider risks are intention-driven, while insider threats happen with the execution of ill intentions. Both the insider stages are harmful to your business operations, and you need to control when an insider is a risk to stop it from leading to threats.
The growing remote work insists on the need, more than ever, to understand workplace activities and stay cautious of malicious intent. A study suggests lacking the right tool to identify suspicious insiders costs companies $200 per employee as compliance remediation cost. It’s always wise to act in time and control internal risks rather than wait for them to do damage.
Common instances indicative of insider risks
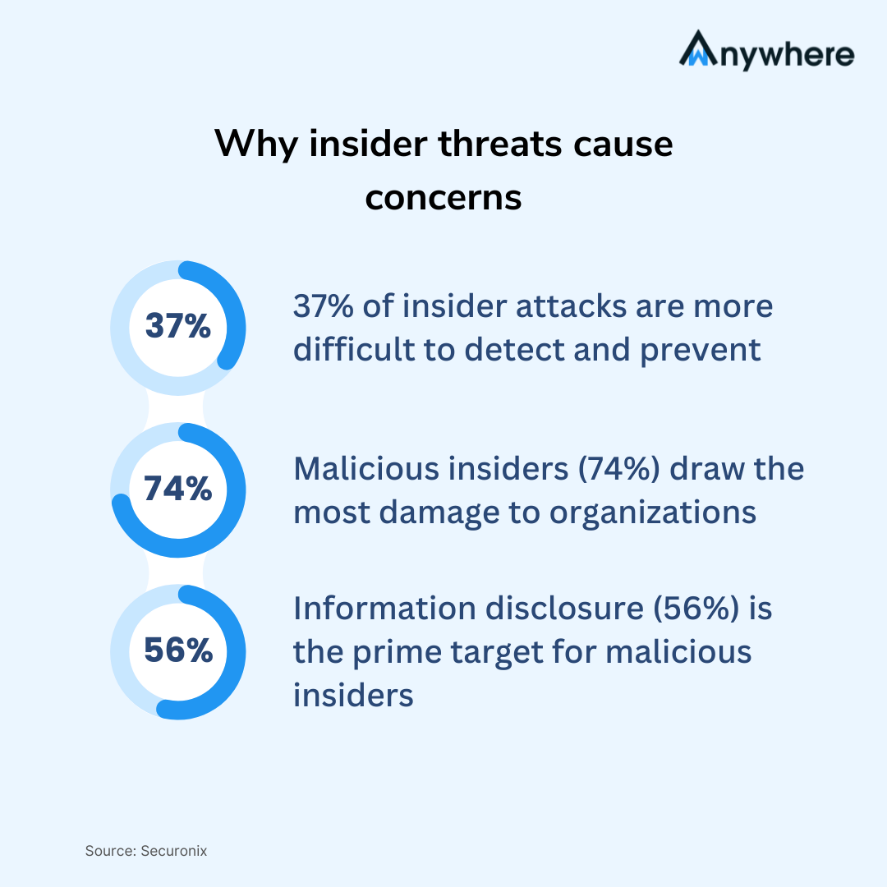
Despite serious concerns about risky insiders in data-sensitive business processes, most organizations (74%) overlook and underfund their insider risk program. The consequences are reflected in increasing insider threats, ignored in their initial stages, costing companies $16.2mn in regulation fines on average.
Let’s discuss what instances hint risk and can lead to threats that concerned organizations should keep an eye on to avoid loss:
Capturing data with copy-paste keystroke
Teams in data-sensitive roles can cause high risks to organizations in the absence of a robust security system in place. Businesses can’t know if teams are taking advantage of their trust and are involved in recording confidential information using copy-paste keyboard actions.
Using mobile devices at work
Employees with recording devices at work can prove fatal to business data integrity. Using screen capture and recording features in portable mobile devices, insiders can steal personal, health, and financial details of customers, violating ISO, HIPAA, and PCI-DSS compliance.
Exposing data to unauthorized persons
Insiders with authorized access to systems, resources, and networks in organizations can leverage the advantage of their authority to breach security and capture vital information for personal gain, inviting hefty non-compliance fines for their companies.
How an insider risk leads to threat
An insider can turn into a risk and later become a threat under the impression of diverse work conditions in an organization. Those conditions can vary from workplace dissatisfaction, non-welcoming members, unsupportive behavior, less growth opportunities, and more. It could leave employees with bad experiences, triggering extreme sentiments in them.
Former employee compromising data
Employees leaving organizations with bad experiences can cause damage by compromising security in business systems, networks, and data centers. Moreover, former employees having functional credentials even after their departure can expose business networks to external threats.
Disgruntled employee exploiting legitimate access
A dissatisfied employee in an organization can exploit the authority to upload crucial business information to some open platform to harm the organizational reputation and incur non-compliance penalties.
Negligent worker violating data privacy unknowingly
Uninformed employees processing business data carelessly can also become reasons for data privacy non-compliance for organizations with no provisions for training opportunities.
The growing instances of insider risks turning into insider threats reflect the absence of a robust security system in organizations with data-centric business operations. A study found that 74% of organizations are concerned about suspicious insiders – having stringent security measures in place, concerned businesses can respond in time to align insiders and help them avoid activities leading to risks or threats.
Let’s find what difference an advanced security system can bring to curb insider threat occurrences in remote and hybrid operating organizations:
Why you need AI-powered wAnywhere security
With advanced AI capabilities to enable security and compliance in distributed workplaces, the future work solutions from wAnywhere, innovated by ShepHertz, can help data-driven businesses in Finance, Healthcare, Contact Centers and BPO industry apply security rules for operational efficiency.
Detect and control malicious intent with automated detection
Integrate AI-enabled security into your business workflows to automate detections against employee behavior indicating risks. Spot risk instances before they turn into threats to help align employee behavior with workplace compliance and ensure operational security.
Stay in sync with workplace activities with screen recording
Leverage live screen recording and map the defined security standards across your workplace to find gaps that cause non-compliance. Utilize real-time screen capturing for predictive analytics to identify and control insider risks before they grow into threats.
Align teams with compliance and data privacy policies
Define and measure workplace standards for your remote and hybrid teams to help them avoid deviating from security regulations. Ensure Clean Desk policy and compliance with leading security norms, including ISO, HIPAA, GDPR, and SOC 2 Type 2 for data privacy and strengthen business operation security.
Regulating workplace behavior can be an effective security practice to help insiders stay focused on business goals and contribute to operational efficiency. Get support from AI-backed industry-leading security and compliance solutions from wAnywhere monitoring tool for workplace regulations. Start your wAnywhere experience today to see what difference it can bring to the way you work.
What is the difference between insider risks and insider threats?
Business insiders acting against security policies – purposefully or accidentally – can cause risks to workplace compliance, and when that risk - if not controlled - gets executed somehow, it poses a threat to business data integrity and trust.
Is insider risk a threat? How wAnywhere security and compliance can help?
Yes, insider risks putting business security at stake are threats and need to be controlled. With advanced AI capabilities for workplace security and compliance, the wAnywhere monitoring tool enables you to integrate real-time screen recording and automated violation detection with your business workflows, so you get workplace behavior-based predictive analytics to detect and prevent threats before they happen.